Cisco Admin Interface
Introduction#
Multi-Factor Authentication (MFA) is an extra layer of security used when logging into websites or apps. Individuals are authenticated through more than one required security and validation procedure that only they know or have access to.
RADIUS is a protocol commonly used to authenticate, authorize, and account for user access and actions. Acceptto™ offers a simple solution for adding MFA to Cisco™ administrative interfaces via its RADIUS solution. This manual illustrates how to configure both a Cisco device and an Acceptto MFA solution
Pre-Requisites#
An Acceptto RADIUS Agent that is configured and connected to your user directory (for example Microsoft™ ‘Active Directory™’) (See this page for the instructions).
A user with administrative privileges for the Cisco device.
Configure the Acceptto RADIUS Agent#
To integrate Acceptto with your Cisco device, you will need to install an Acceptto RADIUS Agent on a machine within your network. This server will receive RADIUS requests from your Cisco device, check with the LDAP server to perform primary authentication, and then contact Acceptto cloud service for secondary authentication.
- Login to the Acceptto RADIUS Agent with an administrative user and open the radius-agent-config.env file with an editor. It is located in the installed directory of RADIUS Agent. RADIUS clients are configured in this setting.
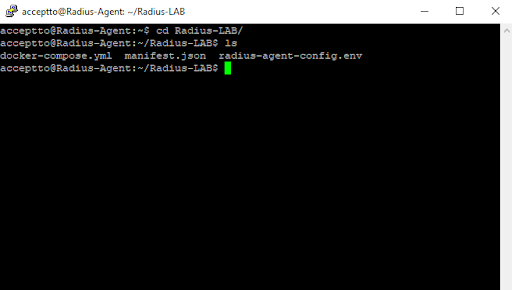
Go to the bottom of radius-agent-config.env file and change the ARA_CLIENTS attribute as follows. The values should be separated by semicolons (;).
ARA_CLIENTS = An optional name for your Cisco device; Internal IP address of your Cisco device; a shared secret
An example configuration might look like this:
ARA_CLIENTS = Cisco;192.168.10.10/32;testing12345
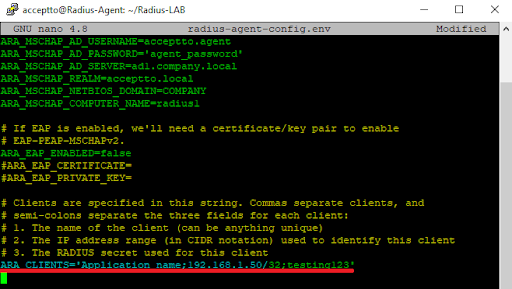
Save file and run the following command for set changes:
docker-compose down && docker-compose up -d
Cisco device configuration#
Log into your Cisco device with an administrative user and type “enable” to gain privileged access.
Enter the configuration mode by typing, “configure terminal.” All the subsequent steps assume that you will remain in this mode.
Create a RADIUS server by typing the following commands.
RADIUS server EXAMPLE address ipv4 [ip address of Acceptto RADIUS Agent] auth-port 1812 acct-port 1813 key [a key provided by your Acceptto RADIUS Agent] timeout 120
Pay attention to the step of setting the authentication and accounting ports. This is extremely important, since by default Cisco uses 1645 and 1646.
Create a RADIUS server group by typing the following commands. (The source interface line is optional, and depends on your internal routing):
aaa group server RADIUS AccepttoRADIUS server name EXAMPLE source-interface [the nearest interface]
Create a login method that uses the newly configured RADIUS group:
aaa authentication login mylogin group AccepttoRADIUS
Creating a new login method may disrupt your operations. You may want to ensure connectivity via another administrative interface or by scheduling a reload after a certain number of minutes.
Associate the login method to one or more administrative interfaces. Yest one of the administrative interfaces before applying it to all administrative interfaces. For example, to test logging in via SSH (assuming your vty numbers are from 0 to 4) issue the following commands.
line vty 0 4transport input sshtransport output sshlogin authentication mylogin
Test Your Setup#
Open a new ssh session to your Cisco device IP and log in with your Active Directory username and password.
Your It’sMe mobile application will receive a push notification.
Approve the push notification. Your ssh login should be complete. If not, proceed to step 4.
If for some reason your login session does not complete, you can remove the authentication method from the administrative interface by typing:
line vty 0 4no login authentication mylogin
Support#
If you require assistance, please email us at support@acceptto.com
Sales#
Want to learn more about our MFA solutions? Contact our Professional Services for a Demo today.
Disclaimer#
All product names, trademarks, and registered trademarks are the property of their respective owners.
All company, product, and service names used in this document are for identification purposes only. The use of these names, trademarks, and brands does not constitute endorsement by the Acceptto Corporation.
Cisco are either registered trademarks or trademarks of Cisco, Inc. and/or one or more of its subsidiaries in the United States and/or other countries.
'Active Directory' are either registered trademarks or trademarks of Microsoft and/or one or more of its subsidiaries in the United States and/or other countries.