Auth0
Introduction#
Acceptto integrates with Auth0 via its SAML solution and provides a single sign-on (SSO) MFA to ensure the convenience of cloud SSO without its potential security risks. Multi-Factor Authentication (MFA) is an extra layer of security used when logging into websites or apps. Individuals are authenticated through more than one required security and validation procedure that only you know or have access to.
Auth0 is built for developers and is a trusted portal. Acceptto adds MFA to Auth0 portal to provide secure login for developers.This document will show step by step configuration to make this happen.
Pre-Requisites#
- An Acceptto account with a configured Identity Provider and LDAP Agent. (See this page for the instructions)
- A user with administrative privileges for the Auth0 panel.
Configure Auth0™ as SAML Service provider#
Download the SAML metadata and certificate for your organization from Acceptto.
Metadata Download at
https://sso.acceptto.com/<myorganization>/saml/download/metadataor view athttps://sso.acceptto.com/<myorganization>/saml/metadataCertificate Download at
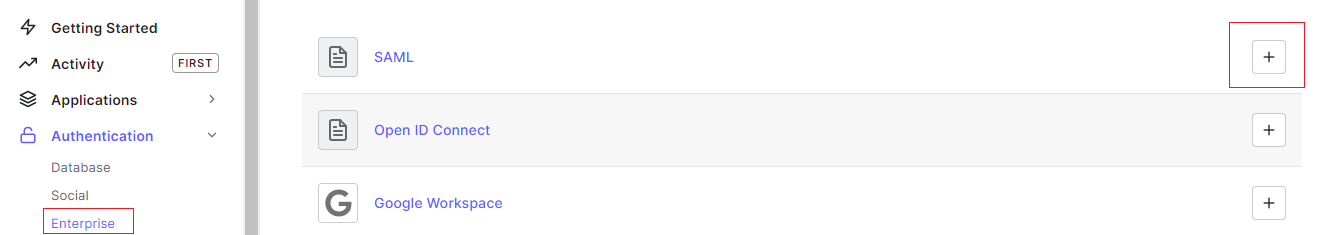
https://sso.acceptto.com/<myorganization>/saml/download/certLog in to your Auth0 instance with a user with administrative privileges. Go to Authentication > Enterprise. Click on Plus in the SAML section.
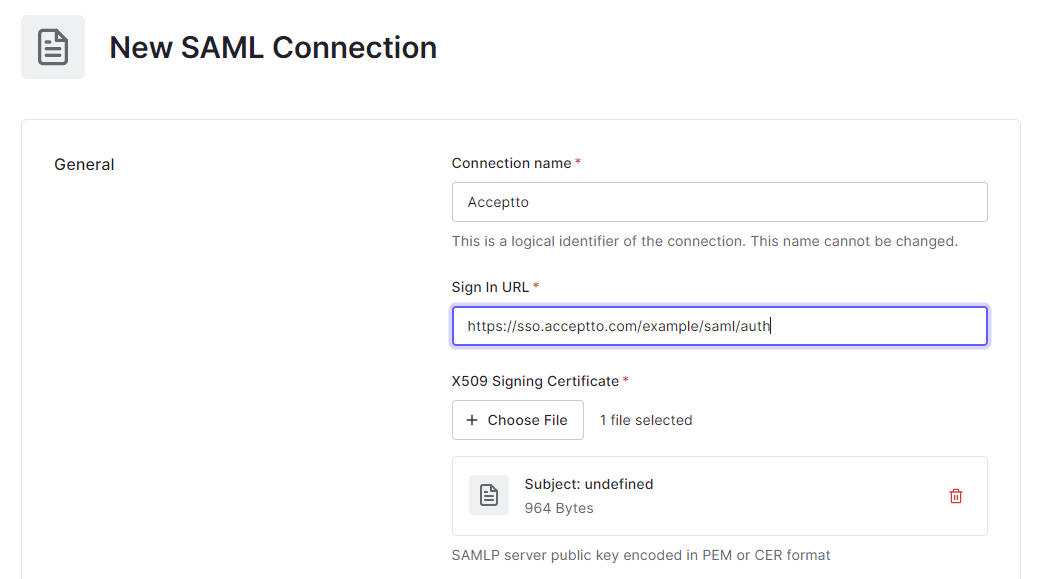
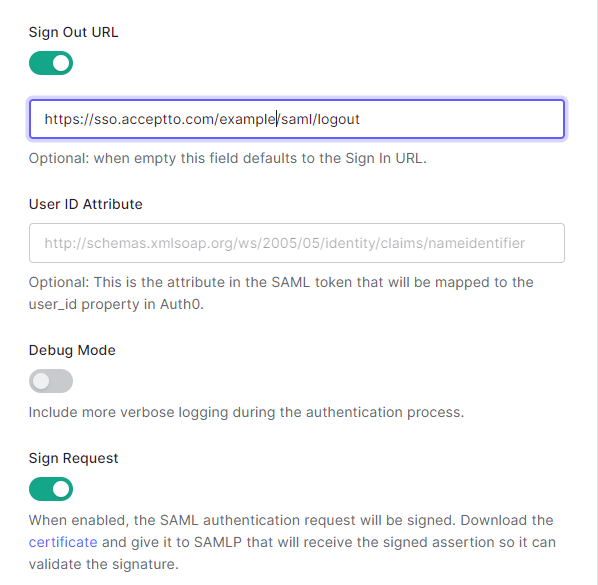
- Fill the form as indicated in the following image and click Save. Get the required information and download the IdP signature certificate from the Acceptto Appliance admin panel in the next section.
- Click on Save Changes.
- Click on Setup and then click Continue.
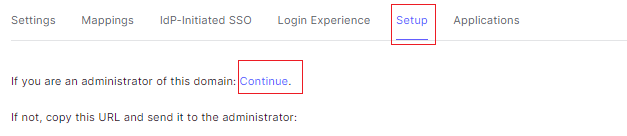
- You can find all the information you need for Acceptto application creation on this page. Copy the links for the next section.
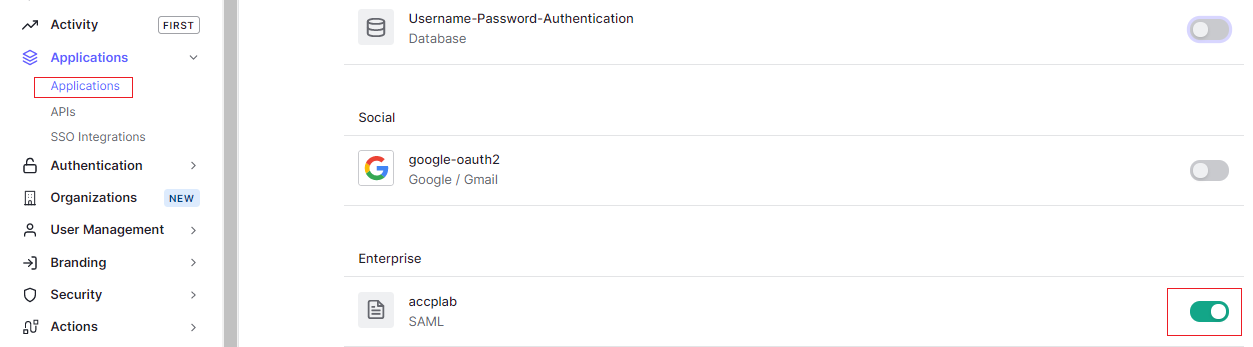
Configure Acceptto as the Connections of Auth0 Applications#
- On the Auth0 admin page, go to Applications and select the desired application.
- On the Connections tab, turn off all sources except Acceptto.
Acceptto SAML Configuration as Identity Provider (IdP)#
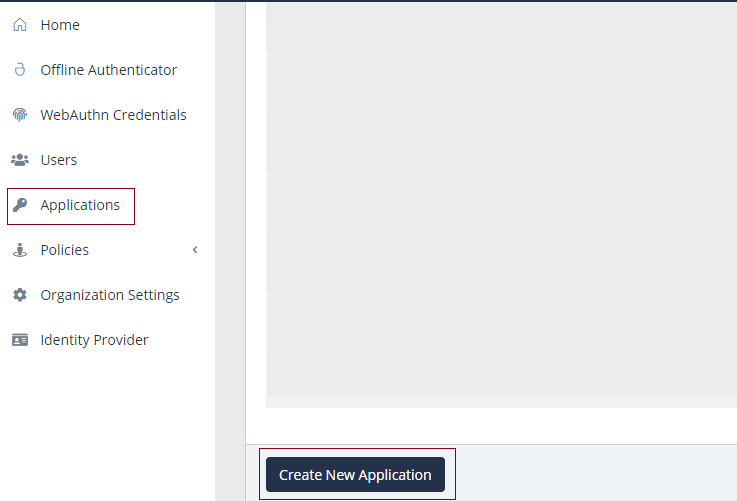
Login to the Acceptto Dashboard with an administrative account and go to Applications.
Create a new application by selecting the Create New Application.
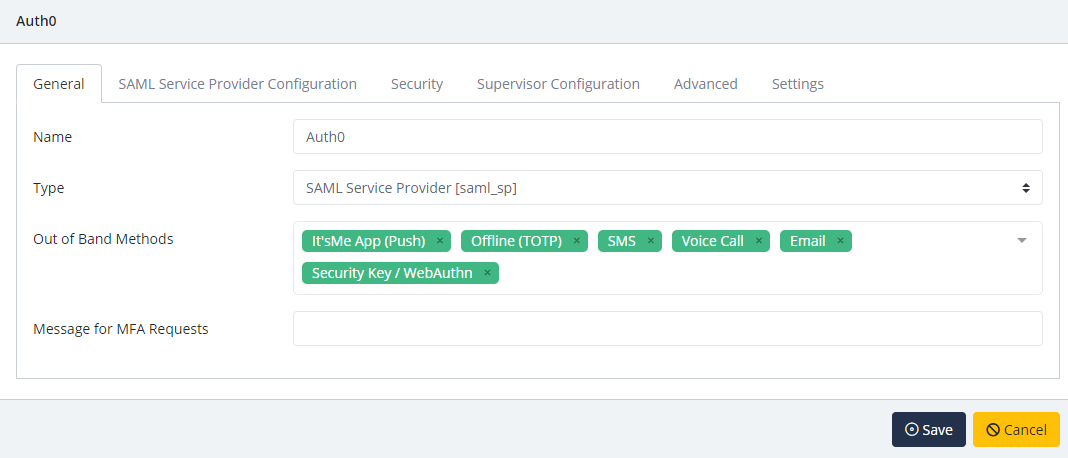
In the New Application form, enter the following values under the General tab.
- Name - The application name displayed in the admin panel (e.g. Auth0)
- Type - Select "SAML Service Provider" from the options
- Out of Band Methods - Select the allowed methods for approving MFA requests
- Message for MFA Requests - Enter the user-facing message for Push, SMS, and email MFA requests (optional)
Under the SAML Service Provider Configuration tab, enter the following values:
- Issuer or Entity ID – Enter the Issuer/EntityID of your Auth0 instance. This value is in the previous section. e.g.urn:auth0:yourdomain:YOUR_CONNECTION_NAME
- Sign in URL - The URL used to login to your Auth0 panel.
- NameID Format - Select "Unspecified" from the dropdown menu.
- Name Identifier - Select "Email" from the dropdown menu.
- Assertion Consumer Service (ACS) URL - Enter the URL which would be like : https:/yourdomain.auth0.com/login/callback?connection=YOUR_CONNECTION_NAME
- Single Logout URL-https://yourdomain.auth0.com/logout
- Algorithm : RSA-SHA256
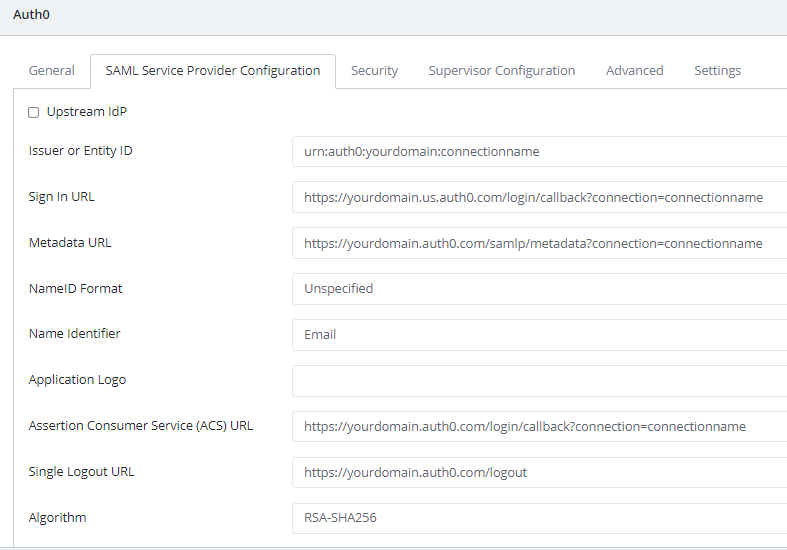
Click Save.
Test Your Setup#
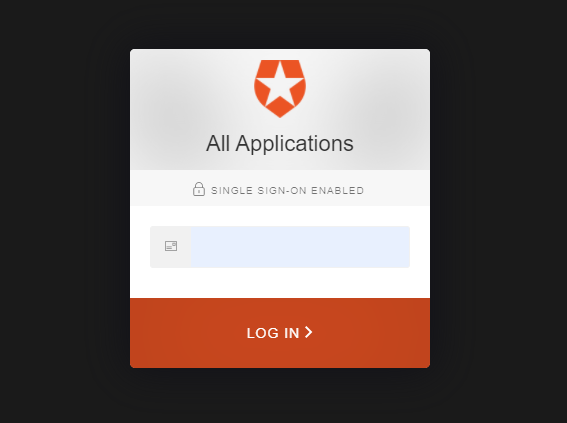
- Run your Auth0 application. You will be redirected to the Acceptto SAML page.
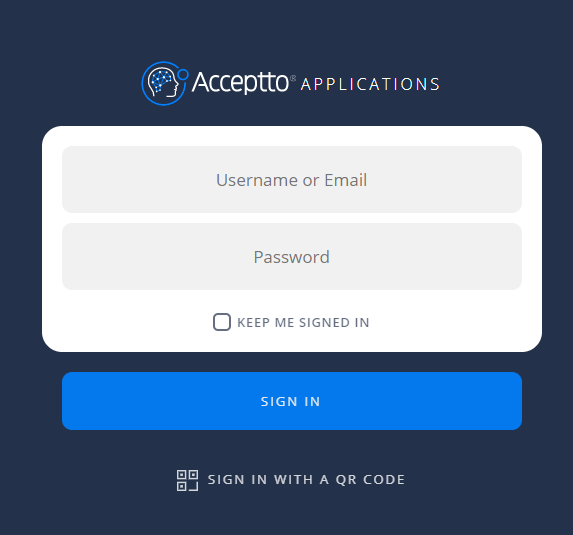
- After successful authentication, you’ll see the Acceptto login page. You can also scan the QR code.
- You are now authenticated with Acceptto SSO-MFA and will be redirected to your Auth0 application page.
Support#
If you require assistance, please email us at support@acceptto.com.
Sales#
Want to learn more about our MFA solutions? Contact our Professional Services for a demo today.
Disclaimer#
All product names, trademarks, and registered trademarks are the property of their respective owners.
All company, product, and service names used in this document are for identification purposes only. The use of these names, trademarks, and brands do not constitute an endorsement by the Acceptto Corporation.