OpenConnect
Introduction#
Multi-Factor Authentication (MFA) is an extra layer of security used when logging into websites or apps. Individuals are authenticated through more than one required security and validation procedure that only they know or have access to.
OpenConnect is an open-source software application for connecting to virtual private networks (VPN), which implement secure point-to-point connections.
RADIUS is a protocol commonly used to authenticate, authorize, and account for user access and actions. Acceptto offers a simple solution for adding MFA to OpenConnect VPN via its Radius solution. This step-by-step integration instruction illustrates how to configure the OpenConnect VPN server and Acceptto RADIUS MFA authentication solution.
Pre-Requisites#
- An Acceptto RADIUS Agent that is configured and connected to your user directory (for example Microsoft™ ‘Active Directory™’) (See this page for the instructions).
- A user with administrative privileges on an OpenConnect server.
Configure the Acceptto RADIUS Agent#
To integrate Acceptto with your OpenConnect server, you will need to install an Acceptto RADIUS Agent on a machine within your network. This server will receive RADIUS requests from your OpenConnect server, check with LDAP server to perform primary authentication, and then contact Acceptto cloud service for secondary authentication.
Login to the Acceptto RADIUS Agent with an administrative user and open the radius-agent-config.env file with an editor. It is located in the installed directory of RADIUS Agent. RADIUS clients are configured in this setting.
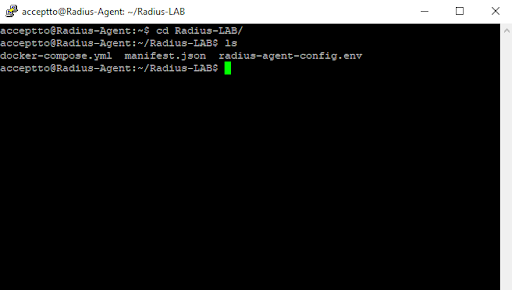
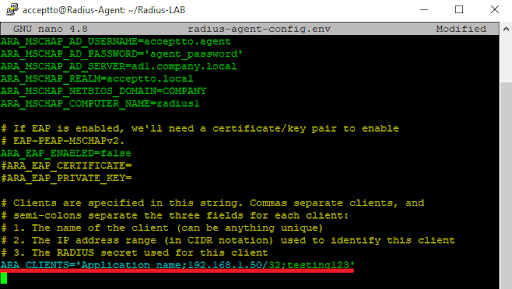
Go to the bottom of radius-agent-config.env file and change the ARA_CLIENTS attribute as follows. The values should be separated by semicolons (;)..
ARA_CLIENTS = An optional name for your OCSERV; IP address of your OCSERV; a shared secret
An example configuration might look like this:
ARA_CLIENTS = VPN;192.168.10.10/32;testing123
Save the file and run the following command to set changes:
docker-compose down && docker-compose up -d
Configure your OpenConnect server#
Login to OCSERV server with administrative privilege.
Open ocserv.conf with a text editor.
sudo nano /etc/ocserv/ocserv.confComment all lines starting with "auth =". It should look like this:
#auth = "pam"
#auth = "pam[gid-min=1000]"
#auth = "plain[passwd=./ocserv.passwd]"
#auth = "certificate"
#auth = "radius[config=/etc/radiusclient/radiusclient.conf,groupconfig=true]"Add a line as follows: auth = "radius [config=/usr/local/etc/radcli/radiusclient.conf,groupconfig=true]"
If you need RADIUS accounting, add a line in the "Accounting methods available" Section: acct = "radius [config=/usr/local/etc/radcli/radiusclient.conf,groupconfig=true]"
Save and exit.
Run the following command for the changes to take effect.
sudo systemctl restart ocservMove to radcli etc folder and open radiusclient.conf with text editor.
nano radiusclient.confConfigure radius settings according to your environment.
nas-identifier “Enter name of your OCSERV” authserver “Enter Acceptto Radius Agent server IP”
servers /etc/radcli/servers
dictionary /etc/radcli/dictionary
default_realm
radius_timeout “60”Save and exit.
Open servers file with text editor.
nano serversEnter the Acceptto Radius Agent and secret like the following: 192.168.5.5 testing 123
Save and exit.
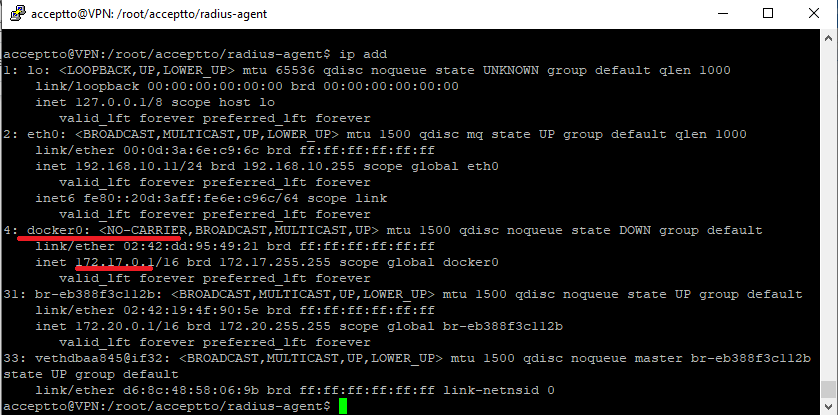
Note: If you installed Acceptto Radius Agent and OCSERV on the same server, in the servers file you must enter the docker IP address of Acceptto Radius agent. This IP address can be find in the following command and screenshot:
Test Your Setup#
Enter the OCSERV server address on the OpenConnect client and insert your username and password. You will receive a push notification on your It’sMe mobile application to authorize access to your VPN server.

Support#
If you require assistance, please email us at support@acceptto.com
Sales#
Want to learn more about our MFA solutions? Contact our Professional Services for a Demo today.
Disclaimer#
All product names, trademarks, and registered trademarks are the property of their respective owners. All company, product, and service names used in this document are for identification purposes only. The use of these names, trademarks, and brands do not constitute an endorsement by the Acceptto Corporation.