Barracuda VPN
Introduction#
Multi-Factor Authentication (MFA) is an extra layer of security used when logging into websites or apps. Individuals are authenticated through more than one required security and validation procedure that only you know or have access to.
RADIUS is a protocol commonly used to authenticate, authorize and account for user access and actions. Acceptto offers a simple solution for adding MFA to Barracuda VPN via its Radius solution. This manual illustrates how to configure both a Barracuda NextGen Firewall device and an Acceptto MFA solution.
Pre-Requisites#
- An Acceptto RADIUS Agent that is configured and connected to your user directory (for example Microsoft™ ‘Active Directory™’) (See this page for the instructions).
- A user with administrative privileges for the Barracuda NextGen Firewall device.
Configure the Acceptto RADIUS Agent#
To integrate Acceptto with your Barracuda NextGen Firewall, you will need to install an Acceptto RADIUS Agent on a machine within your network. This server will receive RADIUS requests from your Barracuda NextGen Firewall, check with LDAP server to perform primary authentication, and then contact Acceptto cloud service for secondary authentication.
- Login to the Acceptto RADIUS Agent with an administrative user and open the radius-agent-config.env file with an editor. It is located in the installed directory of RADIUS Agent. RADIUS clients are configured in this setting.
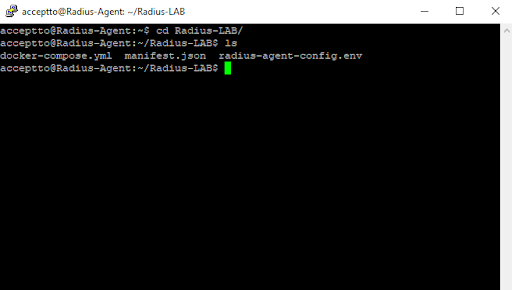
Go to the bottom of radius-agent-config.env file and change the ARA_CLIENTS attribute as follows. The values should be separated by semicolons (;).
ARA_CLIENTS = An optional name for your Barracuda; Internal IP address of your Barracuda; a shared secret
An example configuration might look like this:
ARA_CLIENTS = Barracuda;192.168.10.10/32;testing12345
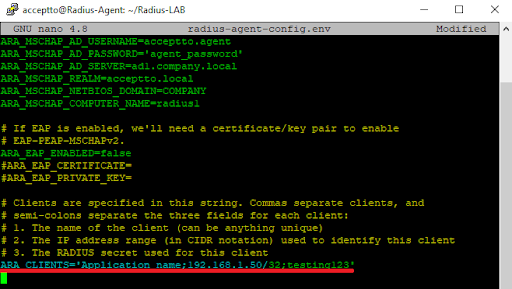
Save file and run the following command for set changes:
docker-compose down && docker-compose up -d
Configure the Barracuda NextGen Firewall#
- Login to the Barracuda NextGen Firewall administrative interface using the NextGen Admin client.
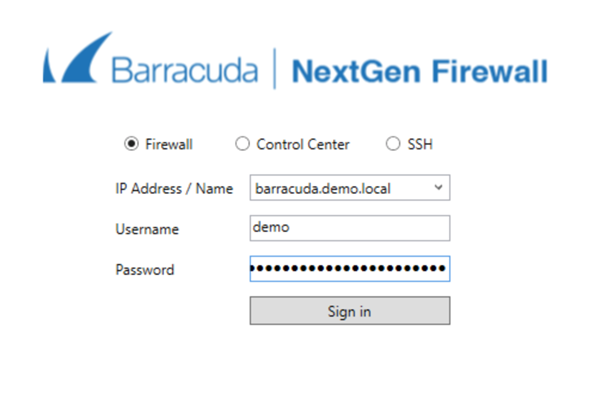
- Navigate to Configuration > Infrastructure Services and Authentication Service.

From the list of authentication methods, select RADIUS Authentication and click the Lock button to enable the configuration of a new RADIUS server.
Click the + sign and add the Acceptto RADIUS Agent IP address to the list of RADIUS servers with the shared secret key between the RADIUS Agent and the Firewall. Note that the timeout of the RADIUS call is increased to 120 seconds to allow the user enough time to allow the multi-factor request.
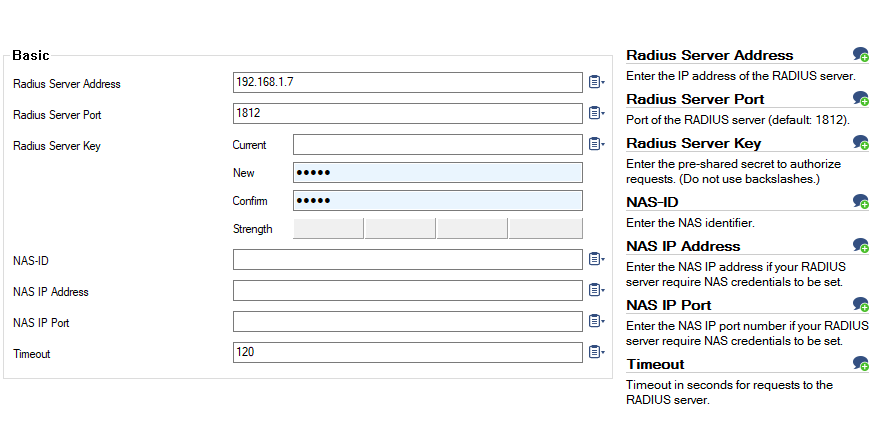
Select Send Changes and then Activate to commit the configuration.
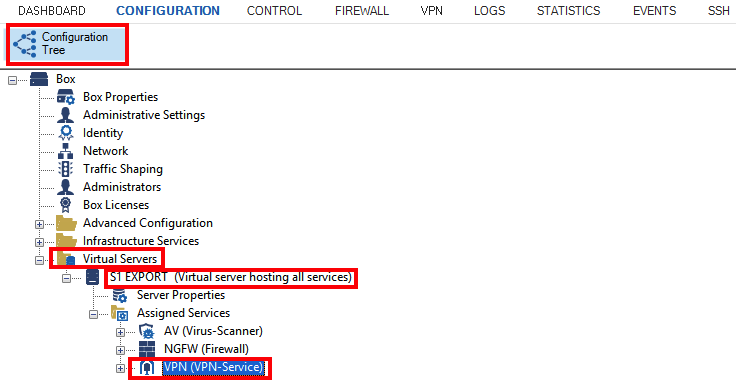
Navigate to the Configuration Tree and Virtual Servers. Then, select a virtual server and VPN (VPN-Services). Note that if the VPN entry does not show up, you will need to add it to the virtual server before proceeding (Right-click on top of the Assigned Services, select Create Service and add a service of the type VPN).
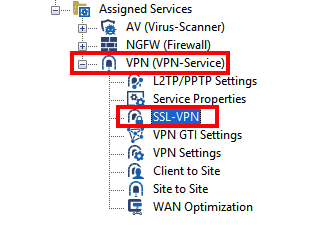
- Expand VPN (VPN-Services) and double-click SSL-VPN to open the VPN setup page.
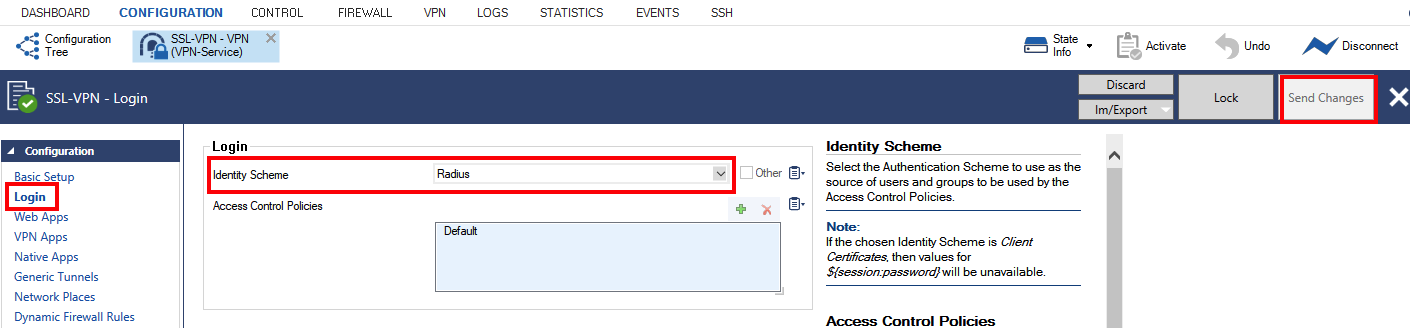
- Select Login. In Identity Scheme, select Radius. Select Send Changes and then Activate to commit the new configuration.
Test your setup#
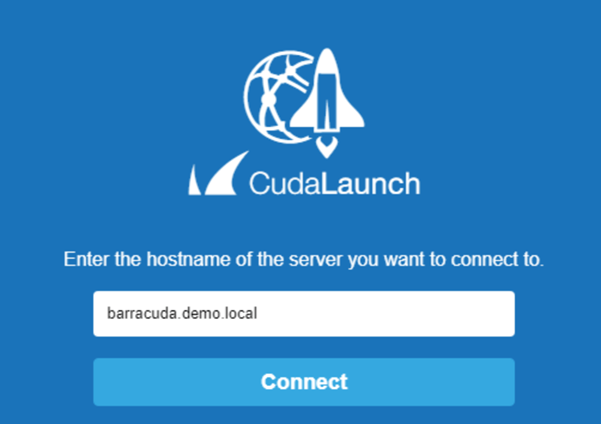
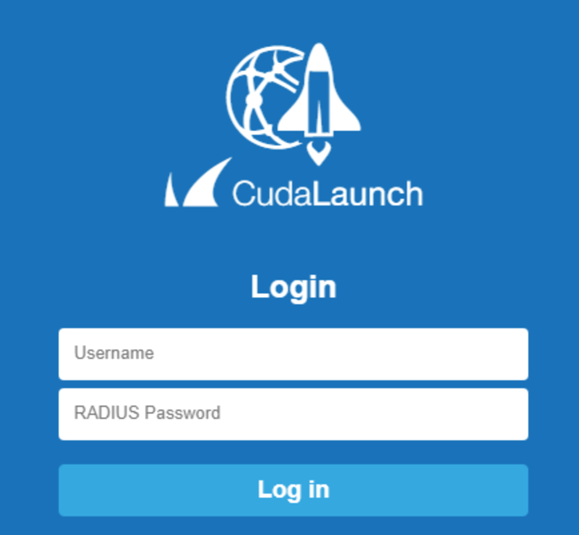
- Launch the CudaLaunch utility and select Connect.
- When prompted, enter your Windows username and password.
- The Acceptto It’sMe mobile application will request approval for login.

After the access is approved, the VPN home page will be displayed.
If the authentication fails to work as expected, you can troubleshoot by running the utility phibstest in the command line of the Barracuda NextGen Firewall:
Display the status of the authentication services
phibstest s | grep radiusThe return should show:
fac_auth_radius_active = 1 fac_auth_radius_busy = 0 fac_auth_radius_error = 0 fac_auth_radius_max = 5 fac_auth_radius_ready = 1 fac_auth_radius_status = ReadyIf the status is not Ready or there are errors, check the log files located at /phio0/logs/. The relevant logs files are box_Control_AuthService.log and box_Firewall_Activity.log.
Test reachability of the RADIUS server by running the command below. Note that if you do not specify the timeout parameter the call to the RADIUS server will time out after 5 seconds.
phibstest 127.0.0.1 a authscheme=radius server=S1 service=VPN user=WindowsUser password=WindowsPassword timeout=120If the connectivity is impaired, make sure that your firewall access list is allowing outbound radius traffic over UDP port 1812
If the authentication between the firewall and the Acceptto RADIUS Agent is failing, ensure that the shared secret is correct.
Support#
If you require assistance, please email us at support@acceptto.com
Sales#
Want to learn more about our MFA solutions? Contact our Professional Services for a Demo today.
Disclaimer#
All product names, trademarks, and registered trademarks are the property of their respective owners.
All company, product, and service names used in this document are for identification purposes only. The use of these names, trademarks, and brands do not constitute an endorsement by the Acceptto Corporation.
Barracuda and Barracuda NG Firewall are trademarks of Barracuda Networks® and/or one or more of its subsidiaries, and may be registered in the United States Patent and Trademark Office and in other countries.
Microsoft and 'Active Directory' are either registered trademarks or trademarks of Microsoft and/or one or more of its subsidiaries in the United States and/or other countries.