OneLogin
Introduction#
Acceptto integrates with OneLogin to provide better security through Acceptto's intelligent Multi-factor Authentication (MFA). Acceptto's intelligent MFA uses many different signals to improve security while reducing friction.
This integration uses OneLogin's Trusted IdP feature to improve the security of users' logins into the OneLogin portal.
Pre-Requisites#
- An Acceptto account with a configured Identity Provider and LDAP Agent (See this page for the instructions.
- A user with administrative privileges for the Acceptto service.
- An organization identifier provided by Acceptto (organization slug).
- A user with administrative privileges for OneLogin.
Acceptto SAML Configuration as Identity Provider (IdP)#
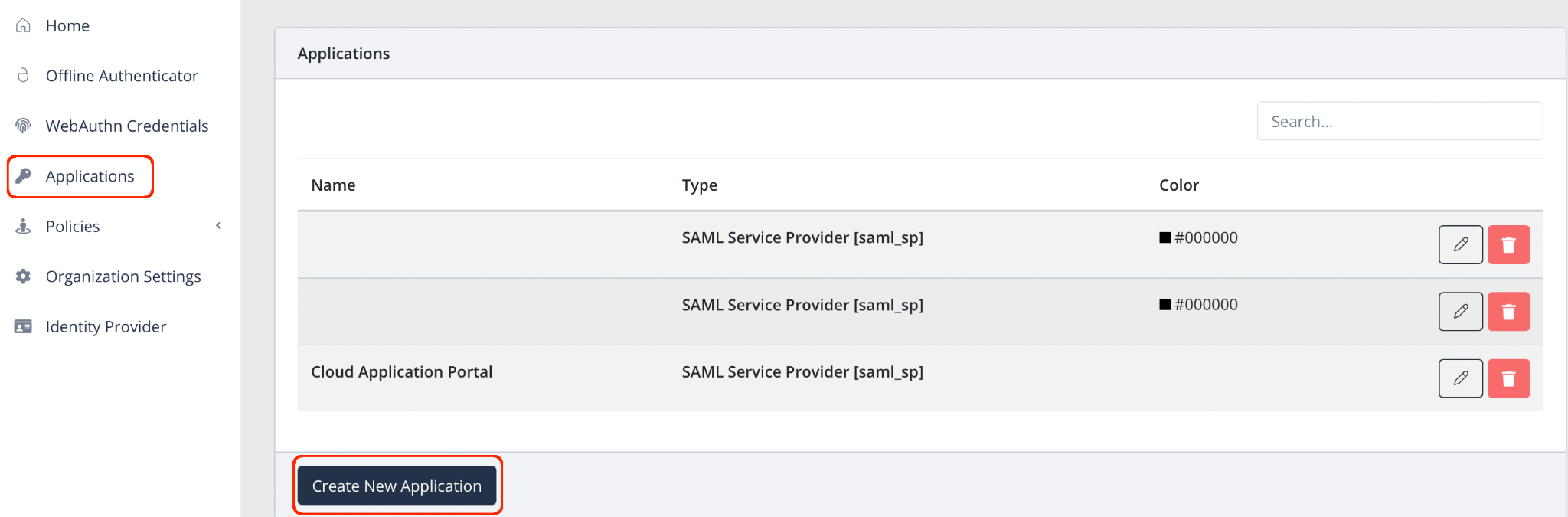
Log into the Acceptto Dashboard with an administrative account and go to Applications.
Create a new application by selecting the Create New Application.
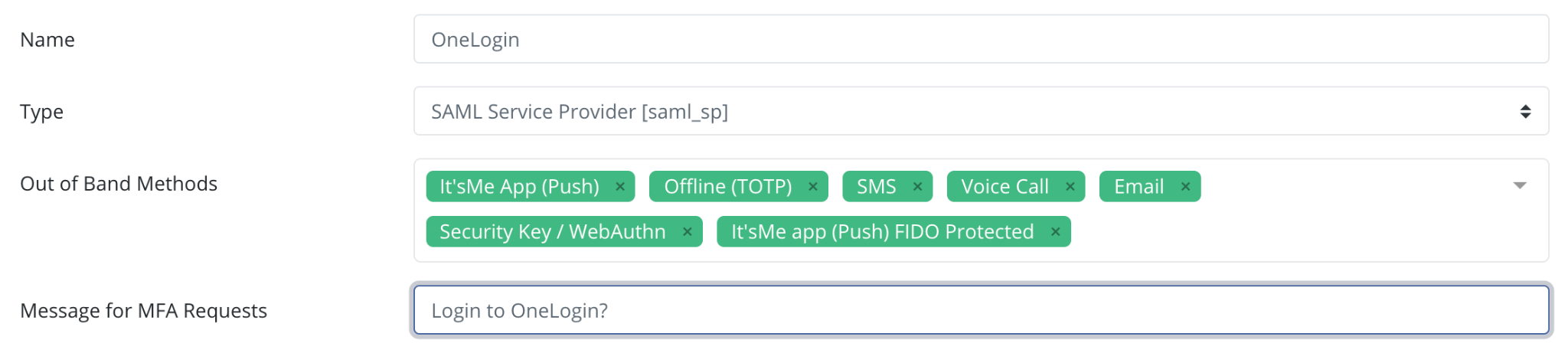
In the New Application form, enter the following values under the General tab.
- Name - The application name displayed in the admin panel and application portal and used for push notifications and audit logs (e.g. OneLogin)
- Type - Select "SAML Service Provider" from the options
- Out of Band Methods - Select the allowed methods for approving MFA requests
- Message for MFA Requests - Enter the user-facing message for Push, SMS, and email MFA requests (optional)
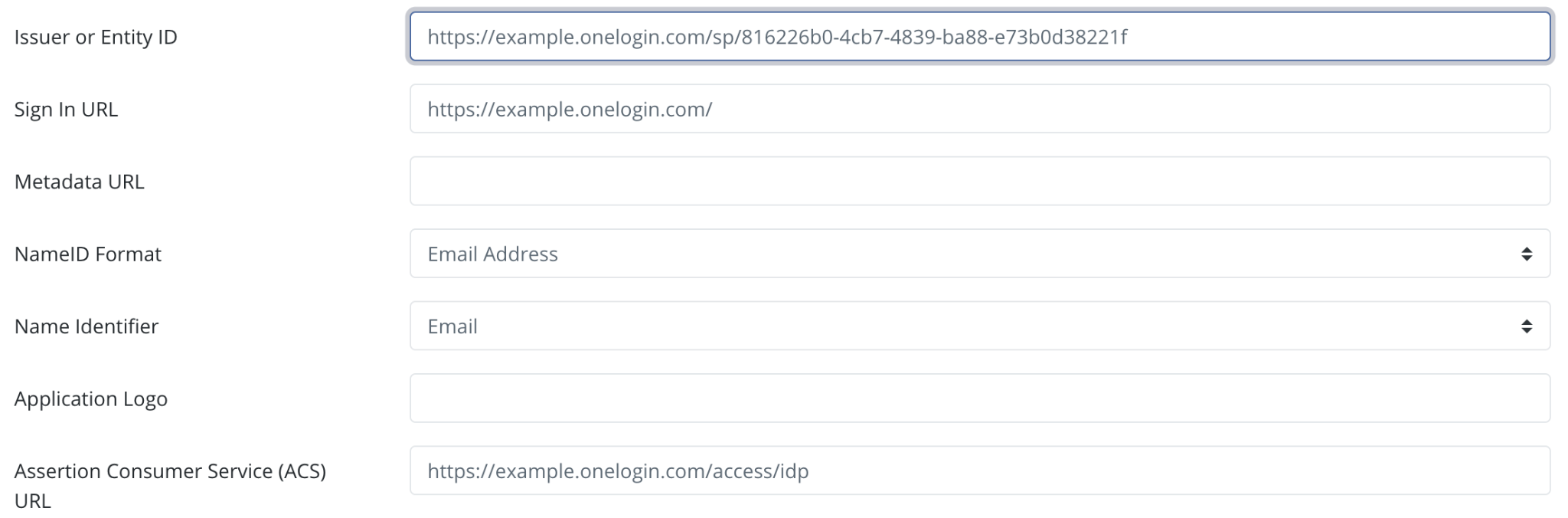
Under the SAML Service Provider Configuration tab, enter the following values:
- Issuer or Entity ID – Enter the Issuer/EntityID of your OneLogin instance. This value is available in the Trusted IdP section of your OneLogin tenant as SP Entity ID (see the next section).
- Sign in URL - The URL used to login to your OneLogin portal (e.g.
https://example.onelogin.com). - NameID Format - Select "Email address" from the dropdown menu.
- Name Identifier - Select "Email" from the dropdown menu.
- Assertion Consumer Service (ACS) URL - Enter the URL on the service provider where the identity provider will redirect to with its authentication response. It should end at access/idp (e.g.
https://example.onelogin.com/access/idp).
Click on the Add New Attribute Assertion button and create the three attributes as shown in the table below. These are mandatory if you want to enable the Just-in-time provisioning feature on OneLogin.
Friendly Name Name Value Email email userPrincipalName Last Name lastname sn First Name firstname cn 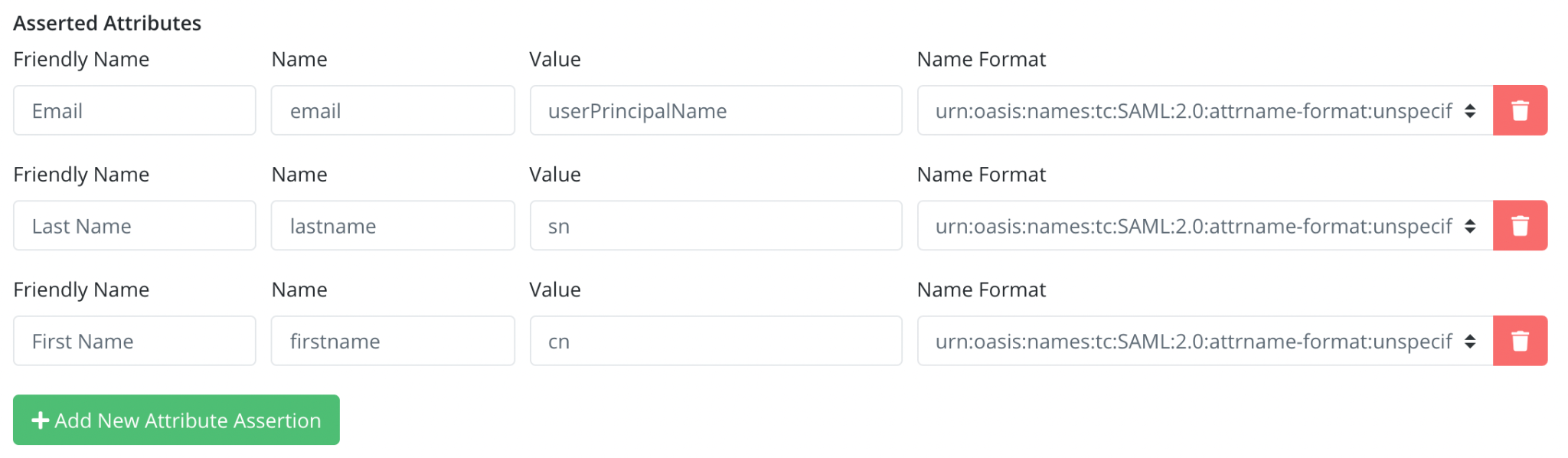
Click Save to create the Application.
Download your SAML IdP X509 certificate. Go to
https://sso.acceptto.com/[organization identifier]/saml/download/certto download the cert.pem file containing your certificate.Download your SAML metadata file. Go to
https://sso.acceptto.com/[organization identifier]/saml/download/metadatato download your metadata file.
Configure OneLogin as a SAML Service Provider#
After creating your Application in Acceptto, log into your OneLogin tenant with an administrative account and add Acceptto as a Trusted IdP as follows.
Go to Authentication > Trusted IdPs and select New Trust.

Click on the gray area under the Trusted IdPs and provide a name for the Trusted IdP configuration.

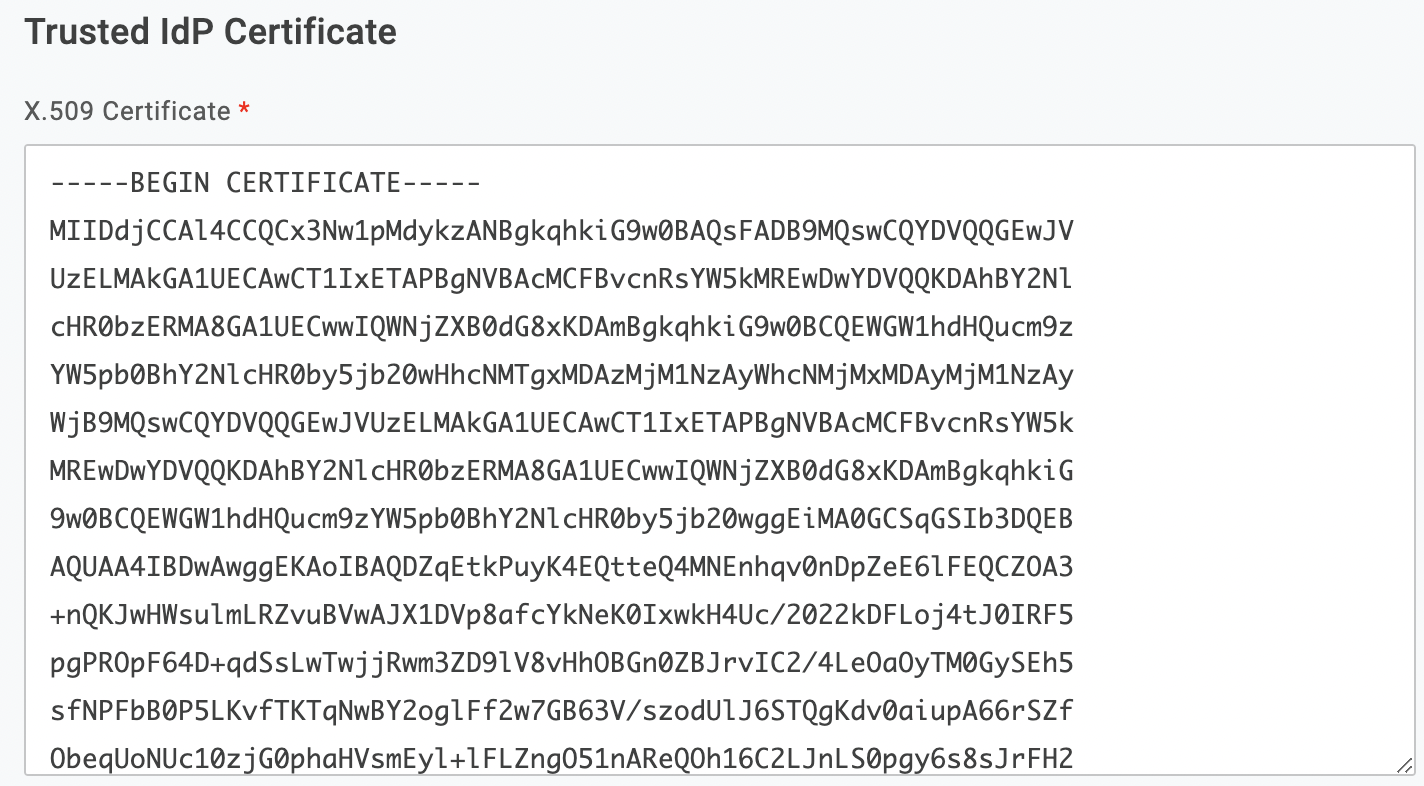
Scroll down and paste the content of the Acceptto certificate you downloaded earlier in the Trusted IdP Certificate section.
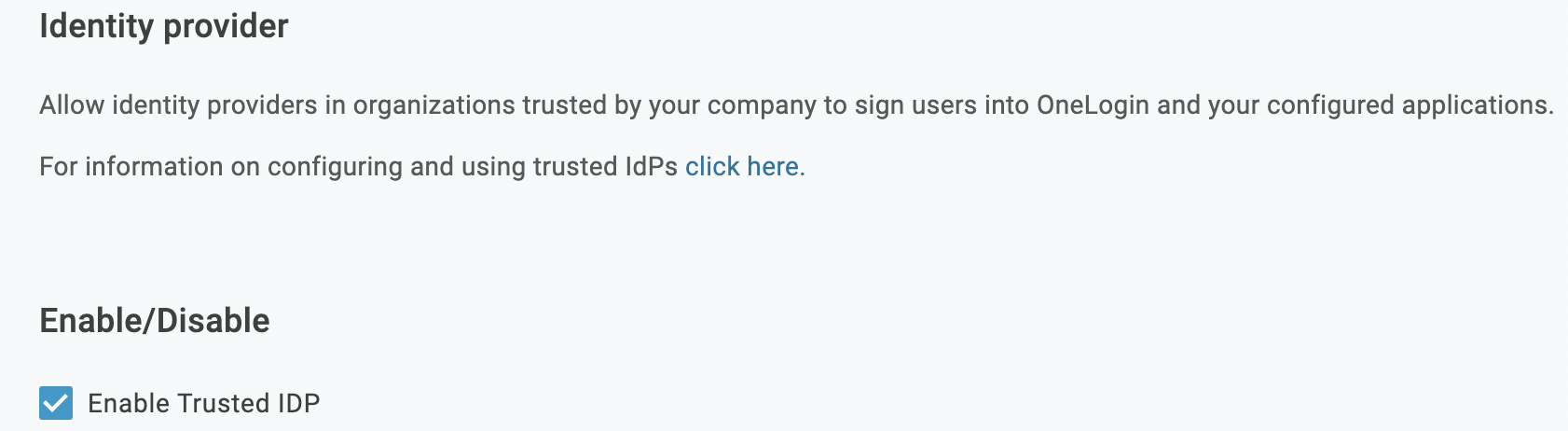
Scroll up and check Enable Trusted IDP in the Enable/Disable field.
If you wish to represent this Trusted IdP as an authentication option on the tenant’s login page via an icon, go to Login Options and check the Show in Login panel. Provide a URL to a suitable icon.
In the Configurations section, enter the EntityID of your Acceptto tenant (find it in the metadata file you downloaded earlier) in the Issuer field.
The Email Domains field is used to automatically invoke this Trusted IdP when a user enters their email address at login time.
Check Sign users into OneLogin. This allows inbound identities from the Acceptto to be matched to local user accounts within the OneLogin tenant, via responses to the
/access/idpendpoint.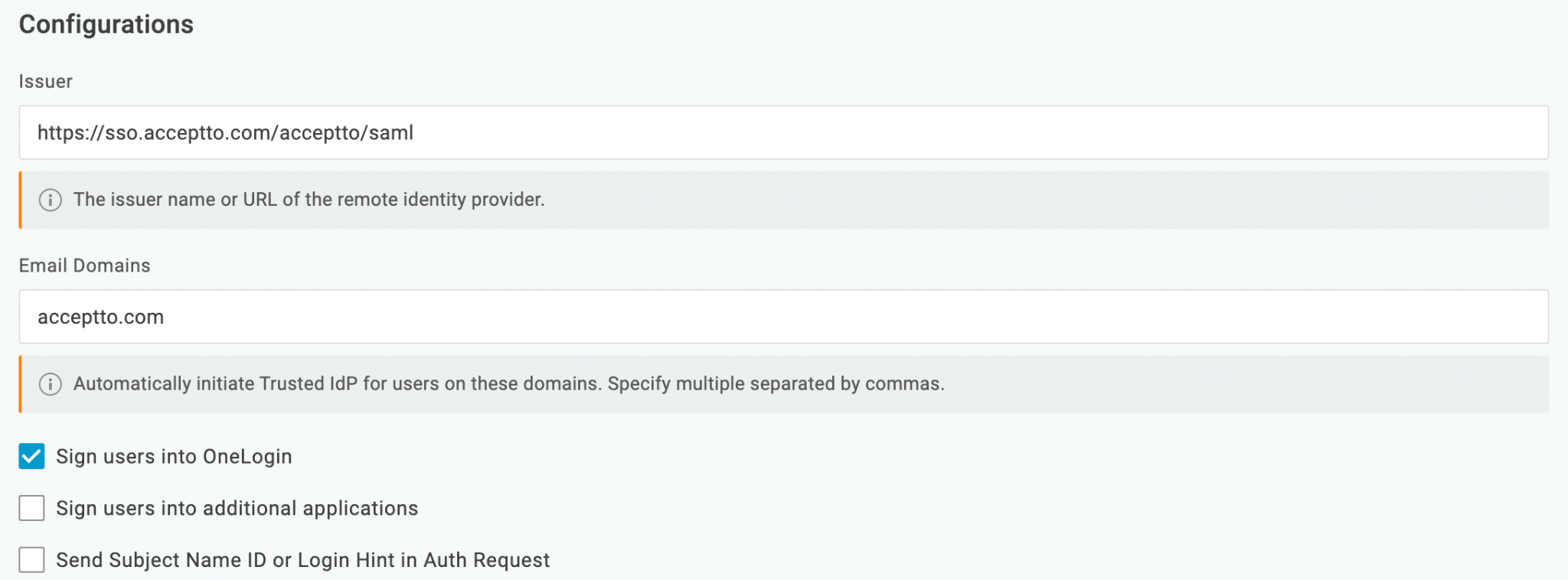
In the User Attribute section, select Email for the User Attribute Mapping.
In the Protocol section, select SAML.
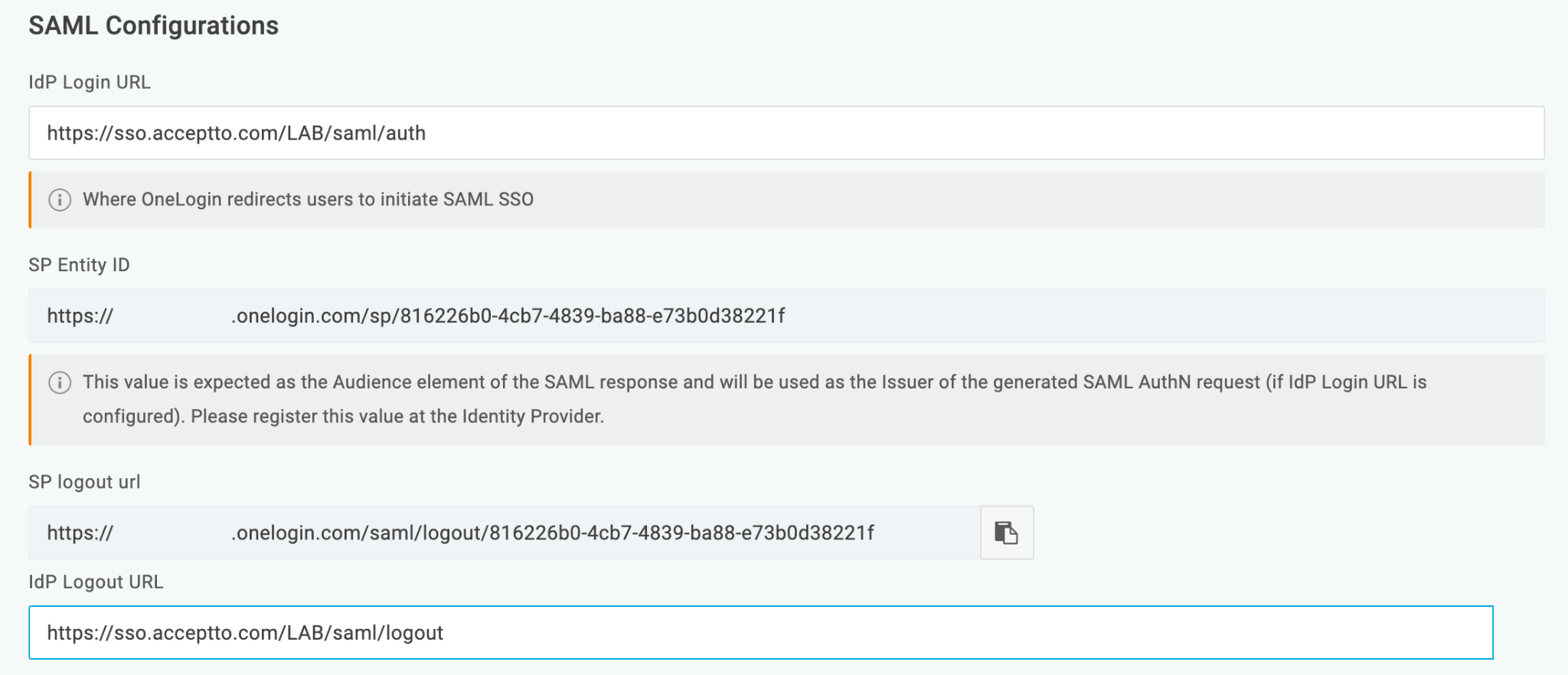
In the SAML Configurations section, enter the SingleSignOnService URL of your Acceptto tenant in the IdP Login URL field and the SingleLogoutService URL of your Acceptto tenant in the IdP Logout URL field (find them in the metadata file you downloaded earlier).
The SP Entity ID is a dynamically-generated, read-only value that must be registered at Acceptto for use as the Issuer or Entity ID.
If you want to create/update user accounts seamlessly at the time of login, based on attributes received from Acceptto, go to the JIT tab.
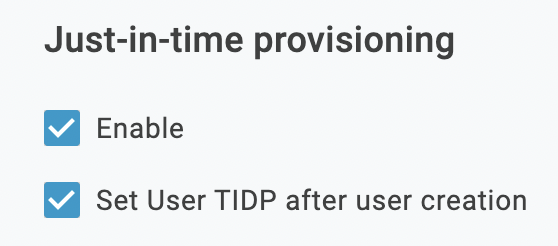
In the Just-in-time provisioning section, check the Enable box. If you want the user record to reflect the Trusted IdP that was used in account creation, check the box to Set User TIDP after user creation.
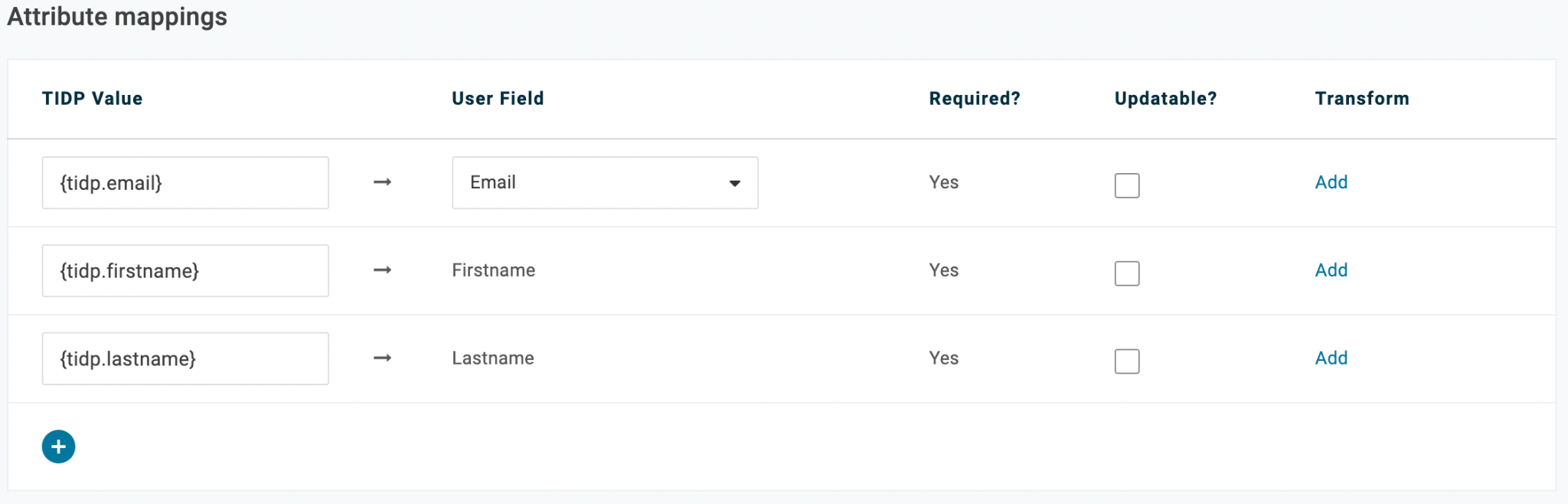
In the Attribute mappings section, create mappings as the image below based on the attribute assertions you created earlier in the previous section. Make sure to use the {tidp.value} format. Click the checkbox for Required if you want to require that attribute. Click the checkbox for Updateable if you want to update the user record with new information when it comes in from Acceptto.
Click Save.
You can make Acceptto the default IdP through the “Set as default Trusted IdP” option in your newly created Trusted IP section.
Test Your Setup#
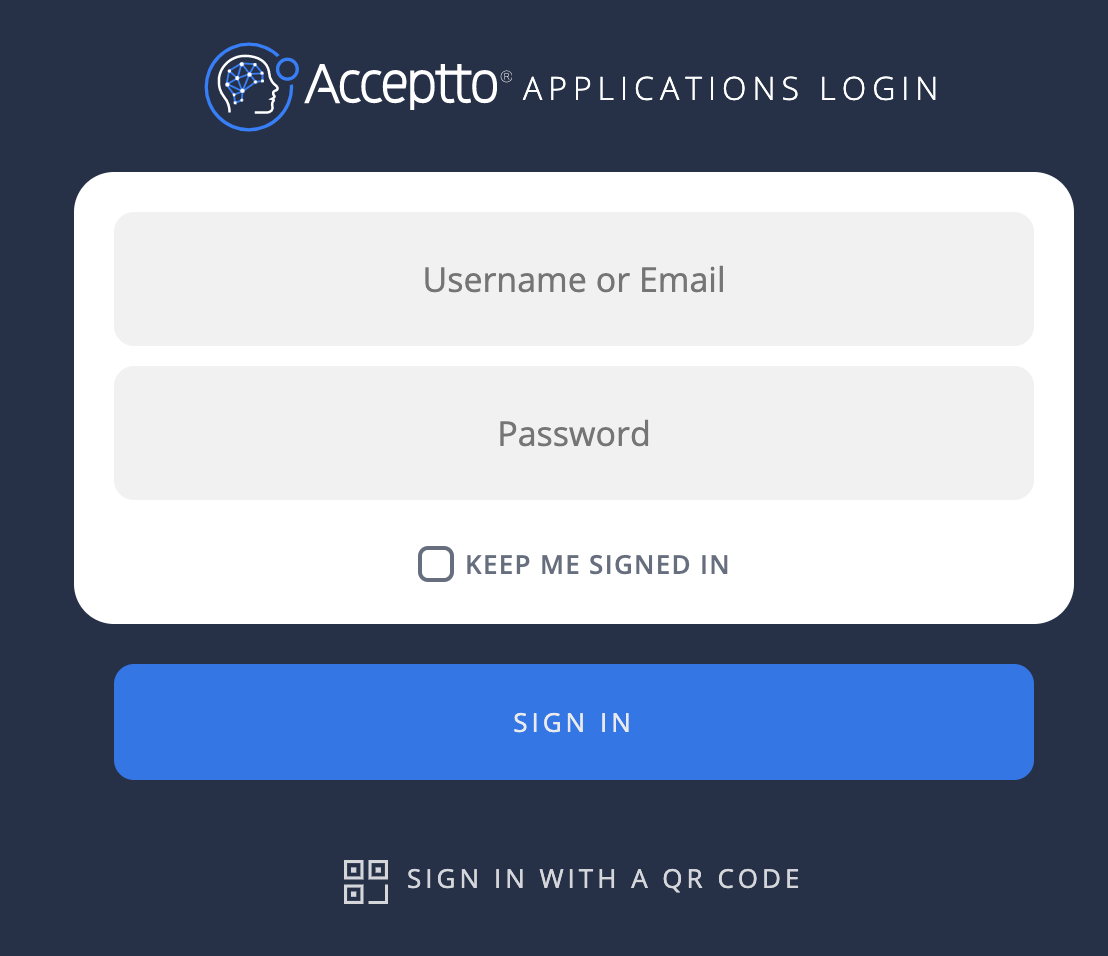
Go to your OneLogin URL through a browser and enter your username.
You will be redirected to the Acceptto SSO page.
After successful authentication, you’ll see the Acceptto MFA options. Select your desired method. Next, approve the authentication request on your It'sMe mobile app.
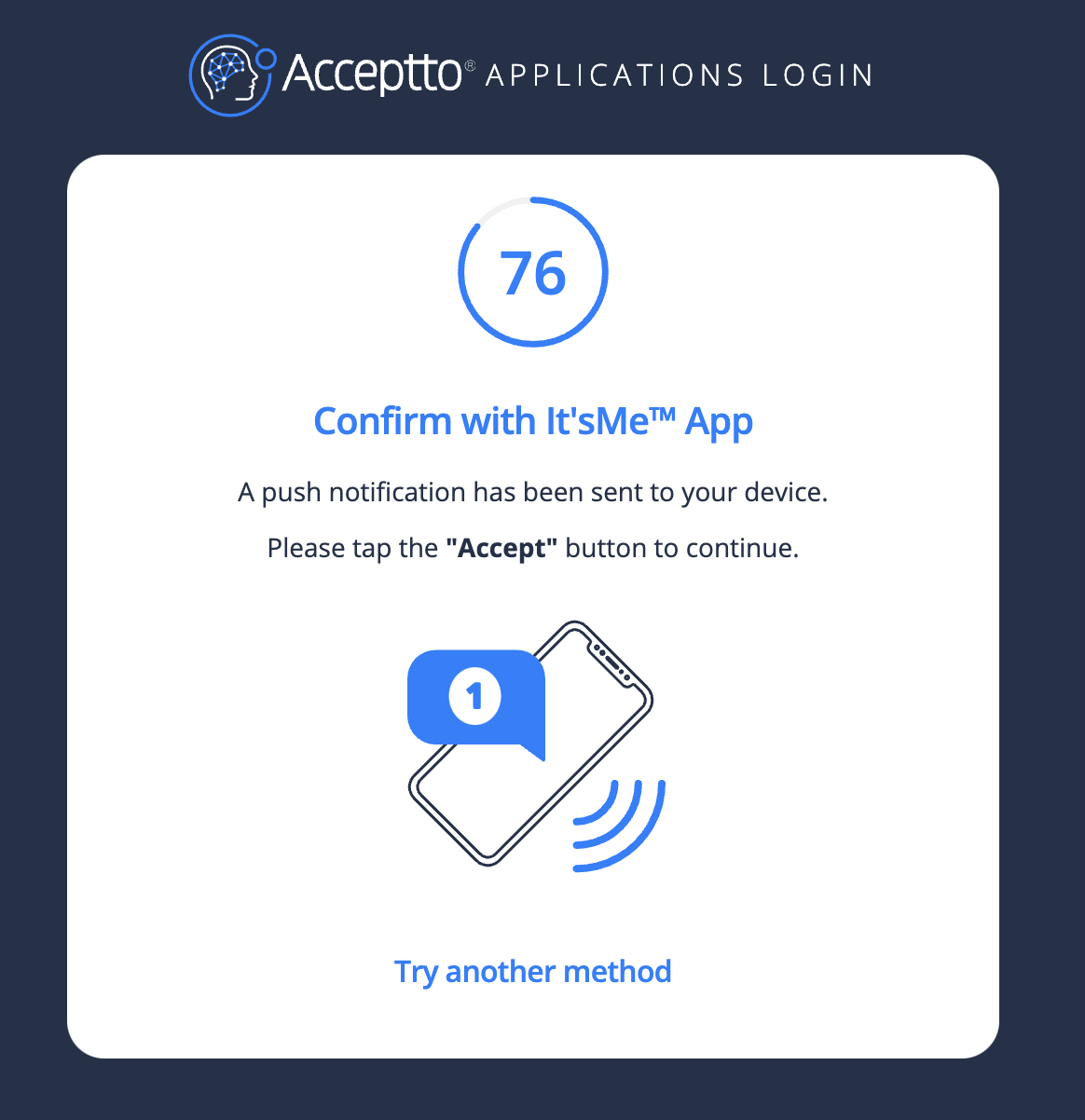
Finally, you will be redirected to your OneLogin portal.
Support#
If you require assistance, please email us at support@acceptto.com
Sales#
Want to learn more about our MFA solutions? Contact our Professional Services for a Demo today.
Disclaimer#
All company, product and service names used in this document are for identification purposes only. Use of these names, trademarks, and brands does not constitute an endorsement by the Acceptto Corporation.